 I'm reading a book on computer crime (How to Prevent Computer Crime by August Bequai) that was published in 1983.
I'm reading a book on computer crime (How to Prevent Computer Crime by August Bequai) that was published in 1983.I'm reading it because I thought it would be interesting to see what people were saying about computer crime twenty or even thirty years ago. I Amazoned some used books on the subject, this one arrived first, and so it's my initial venture into the historical literature of cybercrime.
This particular book is interesting for two reasons.
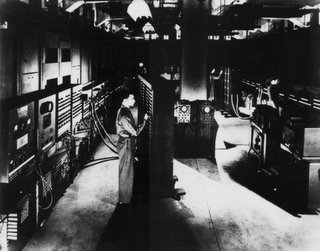
One is that although it was published in 1983, it was clearly written at a time when the notion of the Internet had not entered the public consciousness. The book therefore focuses primarily on what we could call "insider attacks" (more on those below) -- crimes committed by someone who is in physical proximity to the computer or computer system that is involved in the commission of cybercrime.
As a result , the book addresses some activities we do not hear much about today, things like vandalizing a computer by throwing paint on it. It does discuss activities we still deal with, such as using computers to commit fraud, to embezzle funds and to steal trade secrets. It cites a "computer caper" from California in which a gang of "`computernicks'" used their access to computers to provide "improved ratings to consumers with poor credit histories." Bequai, How to Prevent Computer Crime p.41). As far as I can tell (so far), neither the text nor the glossary uses the term "hacker." And while there are references to people having, and using, computers at home, and to businesses using computers to communicate via "telephone lines," there is no treatment of networked crime, such as computer intrusions coming from "outsiders."
The book has what seems, to me, to be a peculiar chapter on "infiltration by organized crime." As far as I know, the Mafia (which is what the book means by "organized crime") has never been a player in computer crime. The chapter suggests (very problematically, IMHO) that the Mafia was using computers to facilitate drug-dealing, loansharking, labor racketeering, thefts of cargo and prostitution. I'm dubious. What is interesting is that the author suggests that "the syndicate" could use computers to extort funds from a business, say, by attacking or threatening to attack its computers. The prediction ultimately came true, though it's not the Mafia we have to worry about in these attacks.
So, one reason the book is interesting is that it is, in effect, quaint . . . We learn how cybercrime was perceived almost a quarter century ago.
The other reason the book is interesting lies in what it can teach us: Since we are so immersed in a network culture, we tend to associate "cybercrime" with outsiders, with hackers who use their computer skills and the Internet to "break into" unsuspecting computer systems and wreak havoc, on some level. Unlike the author of this book, we tend to overlook the threat posed by the insider, by the employee or former employee or temp or consultant who steals company secrets or sabotages data for profit, for revenge or for "fun."
A 2004 study by the U.S. Secret Service and CERT found that the insider threat was a major problem in the banking and financial sector. And a study released at the end of 2005 found that the insider threat is an equally serious problem in Europe.



No comments:
Post a Comment